Viable quantum computers are predicted to be in use in the next few years. Quantum computers can easily break most public-key algorithms, which will create a need for more robust algorithms and crypto-agile systems that can switch their entire public key infrastructure (PKI) to a new algorithm and standard when an attack is detected.

While all crypto algorithms are breakable on paper, the computing power required to do so is incredibly high – this level of technological advancement does not currently exist. However, there have been demonstrations of computers that possess adequate power to accelerate computational speeds enough to break algorithms in a fraction of the time it takes to do so by today’s standards. Therein lies the actual threat of quantum computing – the massive boost to computing speed would render the prime-factorization-based Rivest–Shamir–Adleman or RSA algorithm and Elliptic-Curve Cryptography or ECC easily breakable.
And if the invulnerable RSA and ECC can be cracked, every other algorithm and hash function can eventually be broken. This means the advent of commercial quantum computing (predictably, by 2025) will expose every system in the world to the risk of compromise – quantum cryptography systems and quantum key distribution systems will need to be sufficiently agile to adapt to the evolving threat landscape. Crypto-agility, simply put, is impossible without automation.
Simplify your Public Key Infrastructure (PKI) Updates
Today, we don’t have a quantum computer capable enough to run either of those algorithms, but the impact will be felt almost everywhere when that happens. Without quantum-resistant encryption, everything that has been transmitted, or will ever be transmitted over a network, is vulnerable to eavesdropping and public disclosure.
Some of the significant consequences will include:
- Reputational damage
- Legal costs
- Service disruption
- Financial losses
- Compliance risks
- Intellectual Property (IP) theft, including theft of data
- Theft or loss of personal identity information or PII
- Ransom
- Inability to execute and control sovereignty
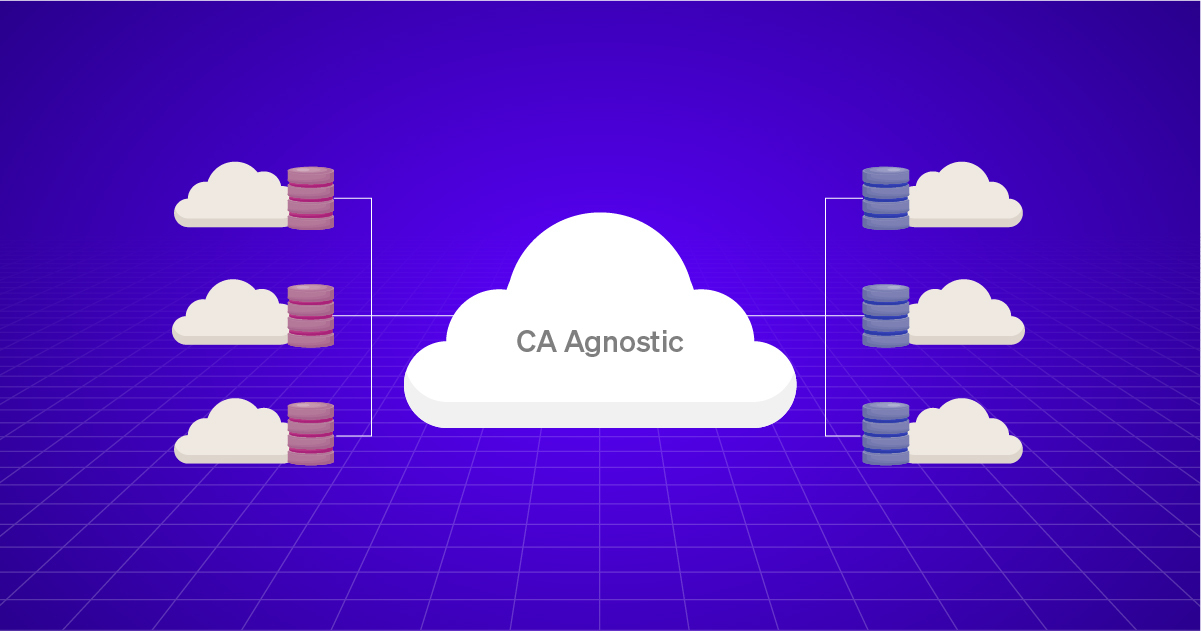
According to Gartner, long-lived PKIs and related systems (10-plus years) must start planning for post-quantum cryptography now and establish crypto-agility strategies for deployments. This means having well-established lifecycle handling in place for both digital certificates and the provisioning of the certificate authority or CA certificates. Quantum computers will break PKI instantly, but the transition period between old and new algorithms will be extended.
It never hurts to be proactive. As a critical first step, identify the starting point. Start with understanding and assessing your risks. Some of the key questions worth considering include:
- Where is your critical data?
- How is it encrypted?
- Is it vulnerable to harvesting?
Also, have a complete understanding of the types of keys present in your infrastructure and their locations. What might help is assessing where you are on the crypto agility maturity model. Determine which algorithms will or will not be suitable for your use cases while analyzing performance characteristics focusing on user experience.
You might look at implementing some of the below-mentioned steps to strengthen data encryption:
- Maximize the entropy in your network: Quantum random number generators deliver full entropy at a high speed
- Use only provable Quantum-Safe encryption algorithms (Symmetric Advanced Encryption Standard or AES)
- Detect and fight eavesdropping, be Quantum-Safe
- Reconsider key length and the frequency of key exchange
- Consider deploying quantum key distribution or QKD on particularly sensitive links
- Stay “crypto-agile” by improving standard AES or migrating to more specific algorithms
- Use the latest encryption key management, with a clear separation of duties
- Use automation to minimize human intervention and focus on a robust key generation and distribution mechanism
- Monitor progress with evaluation and standardization of post quantum or PQ algorithms
- Consider deploying only when you have sufficient confidence in their effectiveness or if there are compliance or regulatory requirements.
The PKI ecosystem can experience turbulence due to a myriad of reasons, and the effects are just as varied. Businesses need to be prepared to face these possible pitfalls while minimizing or eliminating their losses and to do that, they need a PKI that is fully managed, monitored, and accounted for. Poorly managed PKI often marks the entry point for a host of vulnerabilities that could affect productivity, efficiency, and revenue. Ensure that you stay proactive with holistic visibility into your infrastructure.