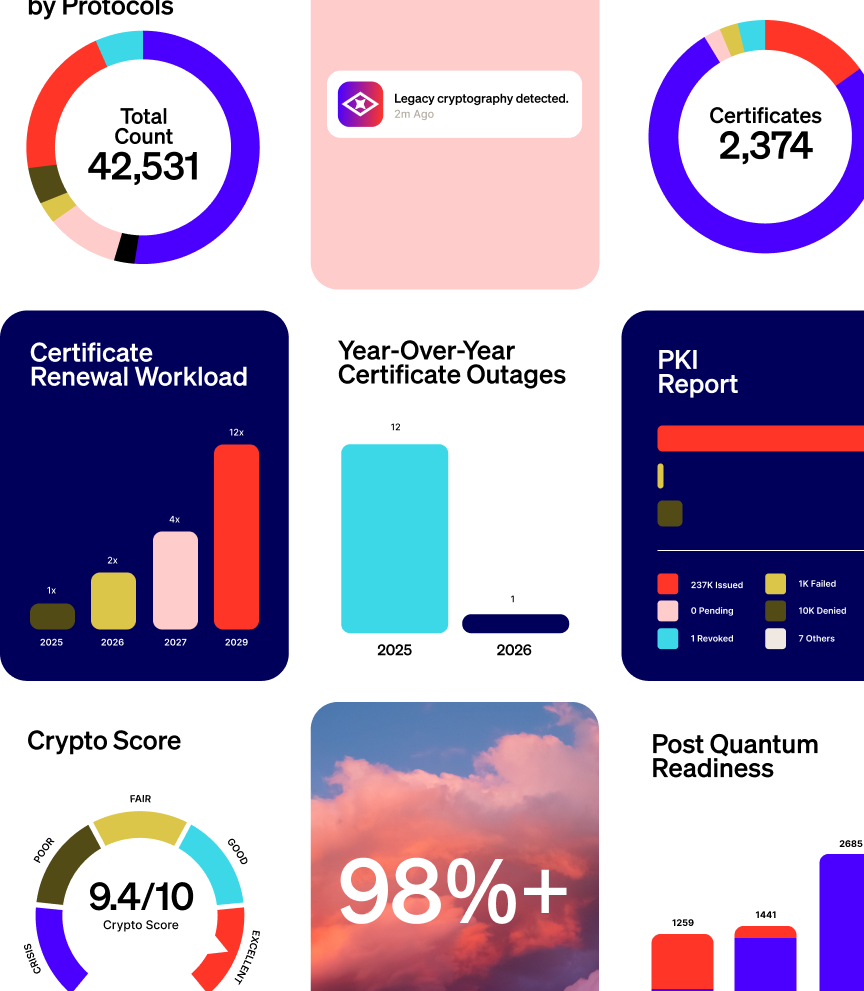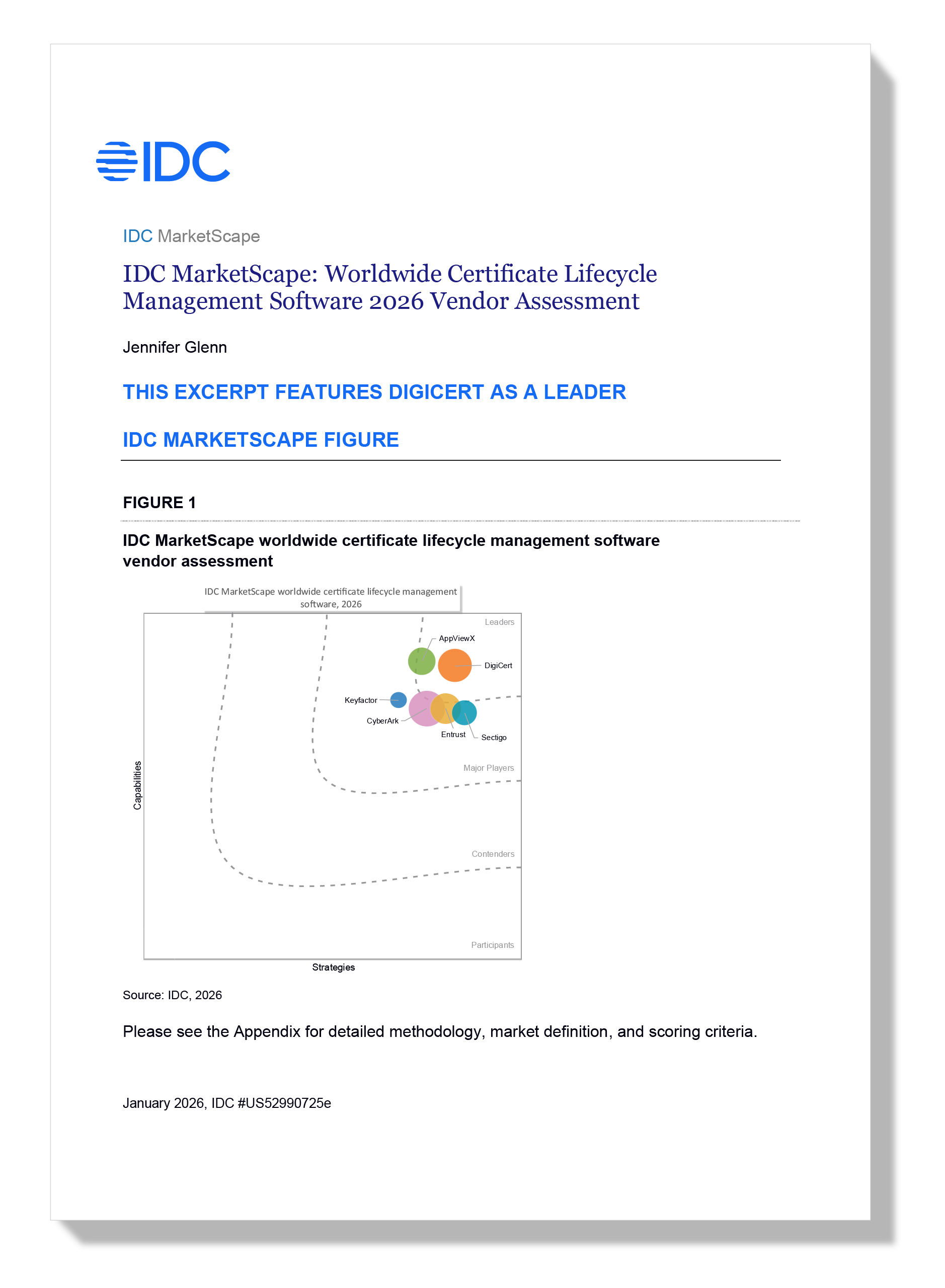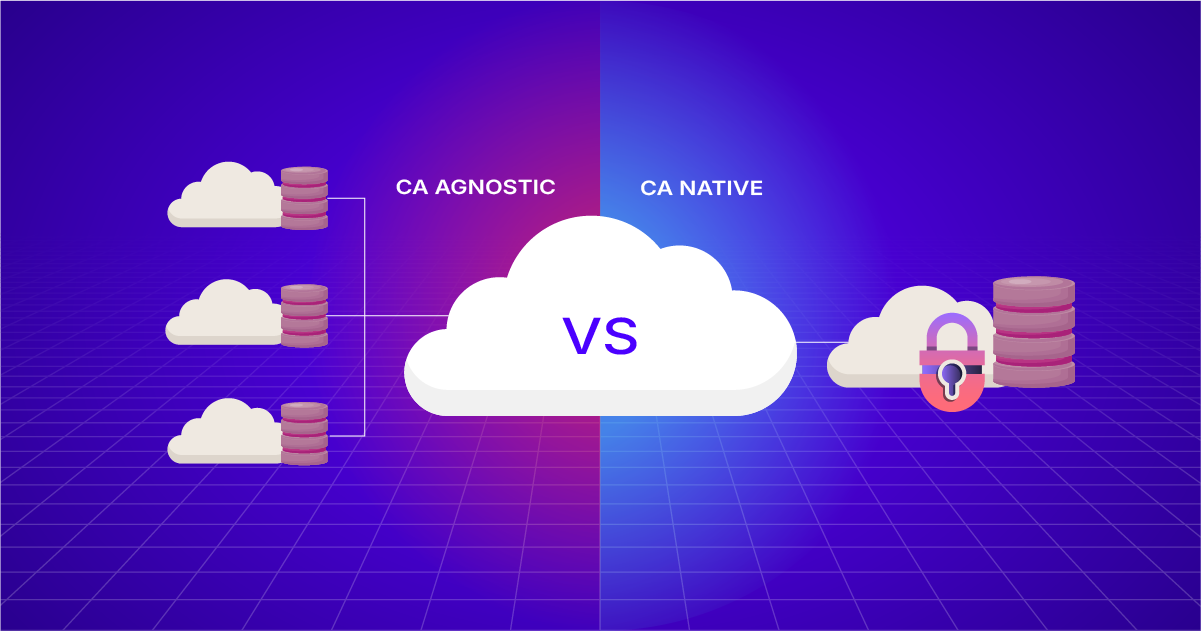
CA-Agnostic vs. CA-Native CLM: A Buyer’s Framework
KNOW MORE →
Let’s Encrypt’s May 13 Changes: 3 Renewal Workflow Updates
KNOW MORE →
What is Non-Human Identity?
KNOW MORE →
Agentic AI Identity Security: Interview with AppViewX’s CTO
KNOW MORE →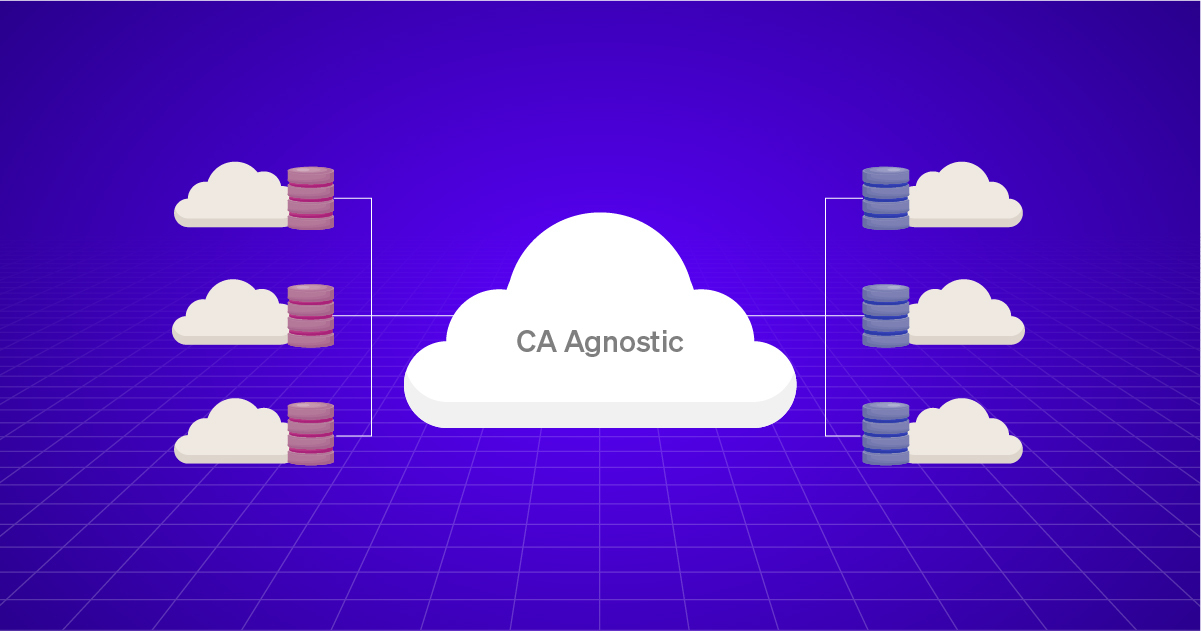
What “CA-agnostic” Really Means: 6 Capabilities To Verify
KNOW MORE →
How to Automate SSL Certificate Renewal
KNOW MORE →
Azure Key Vault Certificate Automation
KNOW MORE →