What is Crypto-agility?
1. What is Crypto-agility?
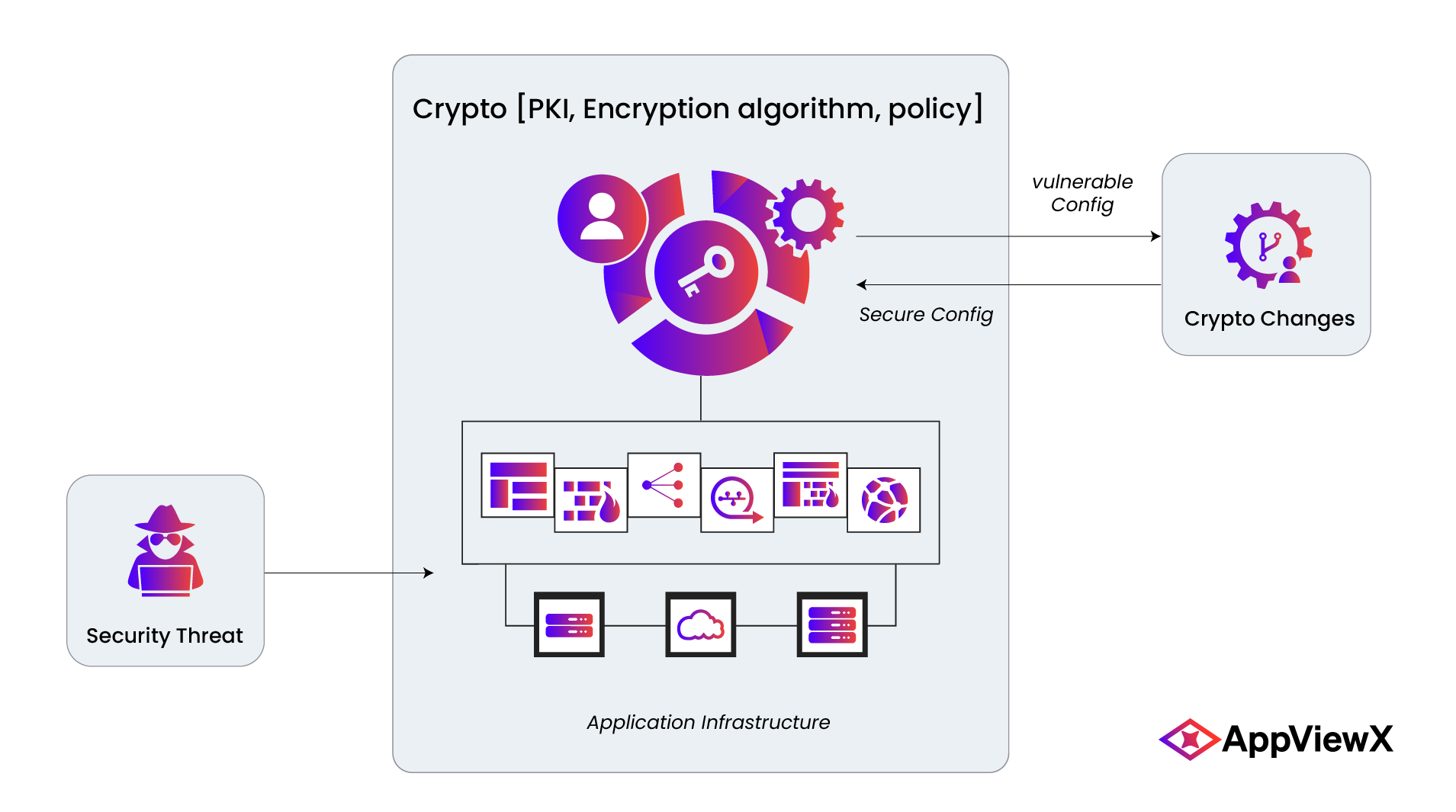
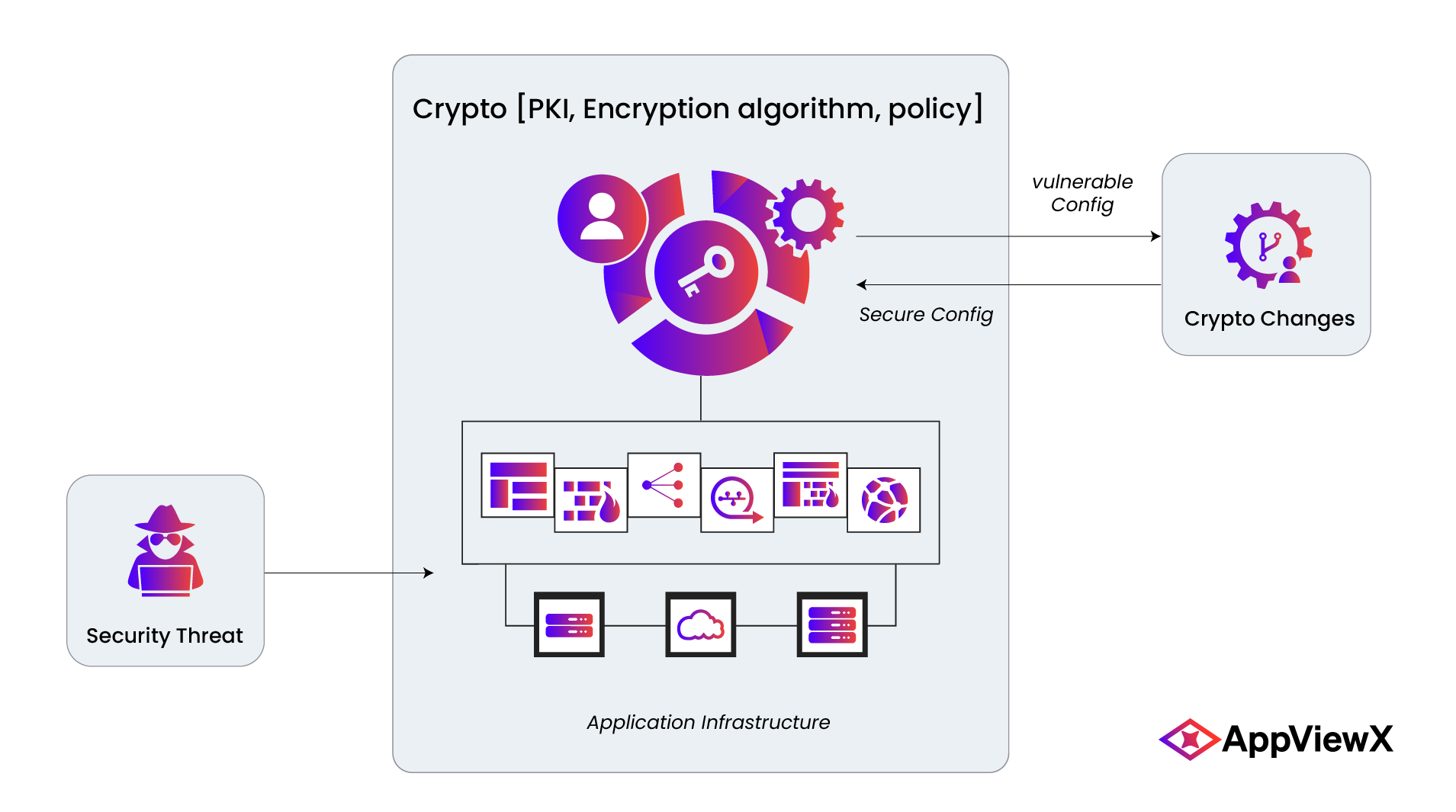
Crypto-agility is defined as the ability of a security system to be able to rapidly switch between algorithms, cryptographic primitives, and other encryption mechanisms without the rest of the system’s infrastructure being significantly affected by these changes.
In other words, it is the ability of an organization to possess complete control over its cryptographic mechanisms and processes, allowing them to make accurate alterations to them without involving intense manual effort. This is an important ability to have, since the principle of accelerating change guarantees that developments in computing power and security will continue to occur at a heightened pace, rendering existing crypto-systems obsolete in a few years unless they are upgraded to the latest version – since threats continue to evolve along with them. Furthermore, with the phenomenon of digital transformation resulting in cryptography being built into virtually every communication system in the world, cryptography cannot remain isolated from other critical systems – making it imperative for administrative teams to have visibility into their crypto-systems in order to effect rapid change when deemed necessary. The looming threat of quantum computing is another compelling reason for organizations to consider becoming crypto-agile.
A robust, cryptographically agile information system will prove to be invaluable to organizations in the long term, and will play a critical role in preventing security breaches, making SecOps teams more efficient, and eliminating monetary losses that may be expended as consulting fees, fines, or remediation costs.
2. Why is crypto-agility necessary?
2.1. Threat Vector: Obsolescence of existing standards
Ongoing cryptographic research suggests that improvements to existing standards will continue to be made, which could be in several months, or several years. While the RSA algorithm has been in use for decades, thanks to how resistant it is to key-cracking, other standards, cipher suites, and hash functions have been phased out and replaced by new ones over the past two decades.
Several examples come to mind, beginning with the aforementioned RSA. RSA-1024, which was the original standard for asymmetric encryption for several years, was replaced by RSA-2048, owing to the lower key length being deemed potentially crackable. The hash functions SHA-1 and MD5 had several vulnerabilities, leading to them being phased out. SHA-1 was eventually succeeded by SHA-2, forcing every organization that leveraged it to make the switch, or risk exposure to hacks. The DES encryption standard too, has been phased out due to its key size being too small to sufficiently protect against attack. More recently, major web browsers deprecated support for the TLS 1.0 protocol, announcing a mid-2020 deadline for all web-facing applications to upgrade to TLS 1.2 or higher.
Today’s leading cryptographic standards like RSA, ECC, and AES will eventually be succeeded by more advanced versions of themselves in the not-too-distant future. When that time comes, and governing bodies like NIST decree that they be updated, it is important for organizations to possess the ability to quickly upgrade all their systems that rely on the deprecated cryptography, lest they risk becoming non-compliant.
2.2. Threat Vector: Quantum Computing
While all crypto algorithms are breakable on paper, the computing power required to do so is incredibly high – this level of technological advancement does not currently exist. However, there have been demonstrations of computers that possess adequate power to accelerate computational speeds enough to break algorithms in a fraction of the time it takes to do so by today’s standards. Therein lies the true threat of quantum computing – the massive boost to computing speed would render the prime-factorization-based RSA algorithm easily breakable (as demonstrated by Peter Shor in 1994). And if the invulnerable RSA can be cracked, every other algorithm and hash function can eventually be cracked as well. This means the advent of commercial quantum computing (predictably, by 2025) will expose every system in the world to the risk of compromise – quantum cryptography systems and quantum key distribution systems will need to be sufficiently agile in order to adapt themselves to the evolving threat landscape.
3. Achieving Crypto-agility
3.1. Best Practices
Crypto-agility is a complex methodology and working towards it will require a multifaceted approach. Changes need to be made to security setups in terms of organizational policy, operating methods, and core technology. PKI will need to be upgraded/altered to support rapid swaps of cryptography, and software development procedures will require modification to incorporate cryptography as well – as opposed to being retrofitted on top of finished software.
The best practices for establishing agile crypto can be split into three tracks:
1) Policy
- Establish and enforce organization-wide policy governing the use, modification, and retirement of cryptographic mechanisms.
- Enforce the use of only the most current versions of cryptography.
- Communicate organizations policy with vendors, resellers, and partners. Provide ample education and training on adherence to these policies, and terminate non-compliant vendors.
- Ensure that vendors provide security updates and patches regularly to comply with guidelines issues by bodies like NIST.
- Define internal role-based access controls to cryptography.
- Update incident response and disaster recovery plans to include provisions for rapid algorithm and protocol swaps.
2) PKI
- Inventory all crypto-resources such as certificates, keys, algorithms, libraries etc. and store them along with perquisite details of operation (for ex: expiration dates for certificates)
- Gain complete visibility into PKI and chains of trust – know exactly where each resource is located and what it is linked to
- Centralize PKI management into a single console
- Have the ability to rapidly identify, replace, and rotate vulnerable PKI without disrupting the endpoints protected by the PKI
- Automate the management, rotation, and testing of PKI
- Enable remote updation via secure controlled access to PKI
- Create backup plans for CA compromise by creating arrangements with alternate vendors, and have the ability to carry out a quick CA migration.
- Have the ability to audit PKI changes and track them centrally.
3) General Strategy
- Create service software layers or gateway applications to interface with security operations to simplify access and control.
- Introduce crypto-agile methodologies into development/DevOps workflows by accelerating crypto-swaps and PKI management.
- Ensure that ownership of crypto assets is adhered to.
3.2. Technological Measures
- Supplement RSA implementations with ECC (Elliptical Curve Cryptography) wherever possible for added security.
- Use high RSA key lengths for symmetric ciphers (>256) – high key lengths in general
- Use large bit sizes for hash algorithms
- Avoid hard-coding of cryptography into applications, algorithms, etc.
Let’s get you started on your certificate automation journey