Excerpts from 2022 Ponemon Report: Certificate Lifecycle Management in Global Organizations
Gone are the days when enterprises exclusively guarded their data centers on-premises. With the introduction of the cloud and its various benefits, enterprises have increasingly adopted a hybrid approach to hosting their applications. In fact, most enterprises today use a hybrid strategy for their data centers, with an average of three or more different clouds driving various applications in their infrastructures. And, the problem lies here.
These different applications distributed across various on-premises and cloud servers require an SSL/TLS certificate to establish trust online. Thus, enterprises end up managing hundreds or even thousands of digital certificates and their private keys in their hybrid network infrastructures. And, when this is mainly done using traditional management techniques like spreadsheets certificate protection, not just management, it gets complicated.
A study sponsored by AppViewX and conducted by the Ponemon Institute© reveals why investing in digital identity management is crucial. The study goes deeper and unearths some interesting industry trends.
As part of the study, approximately 1,600 IT and IT security practitioners across industries were interviewed about the importance of managing digital identities. These professionals reside in North America, Europe, and the Asia Pacific and have deep expertise in identity and access management (IAM) programs, digital transformation initiatives, digital identity management, and certificate lifecycle management (CLM) programs.
Key Findings
Services were far more likely to have one or more security incidents or data breaches due to a digital certificate compromise.
- Sixty-four percent of respondents in services experienced a security incident or data breach in the past two years.
- The lowest occurrence is in retail (42 percent of respondents) and public sector (39 percent of respondents).
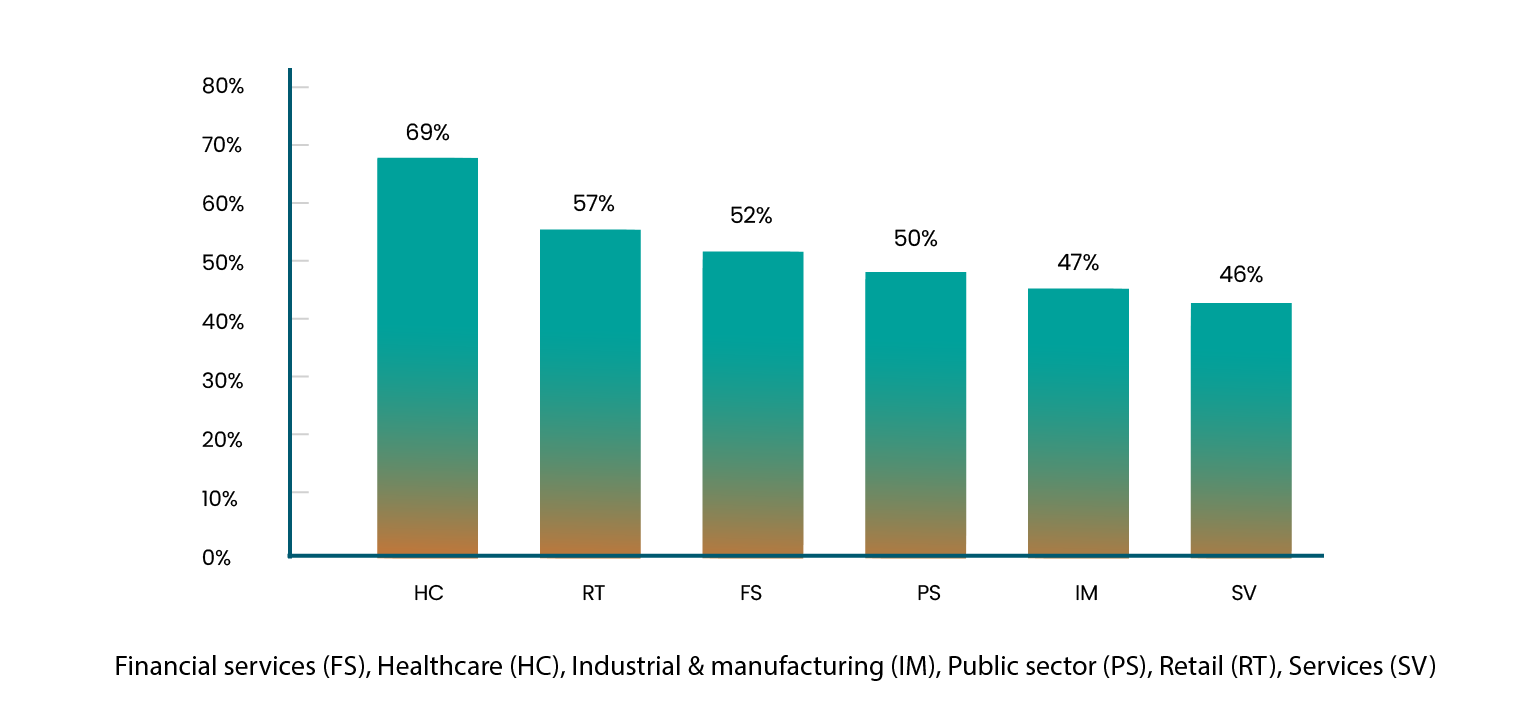
Healthcare and retail are most likely to invest more in managing certificates and keys than human identities, 69 percent and 57 percent of respondents, respectively. The financial services vertical is the next to follow, according to 52% of respondents.
Industries investing more in managing certificates and keys than human identities
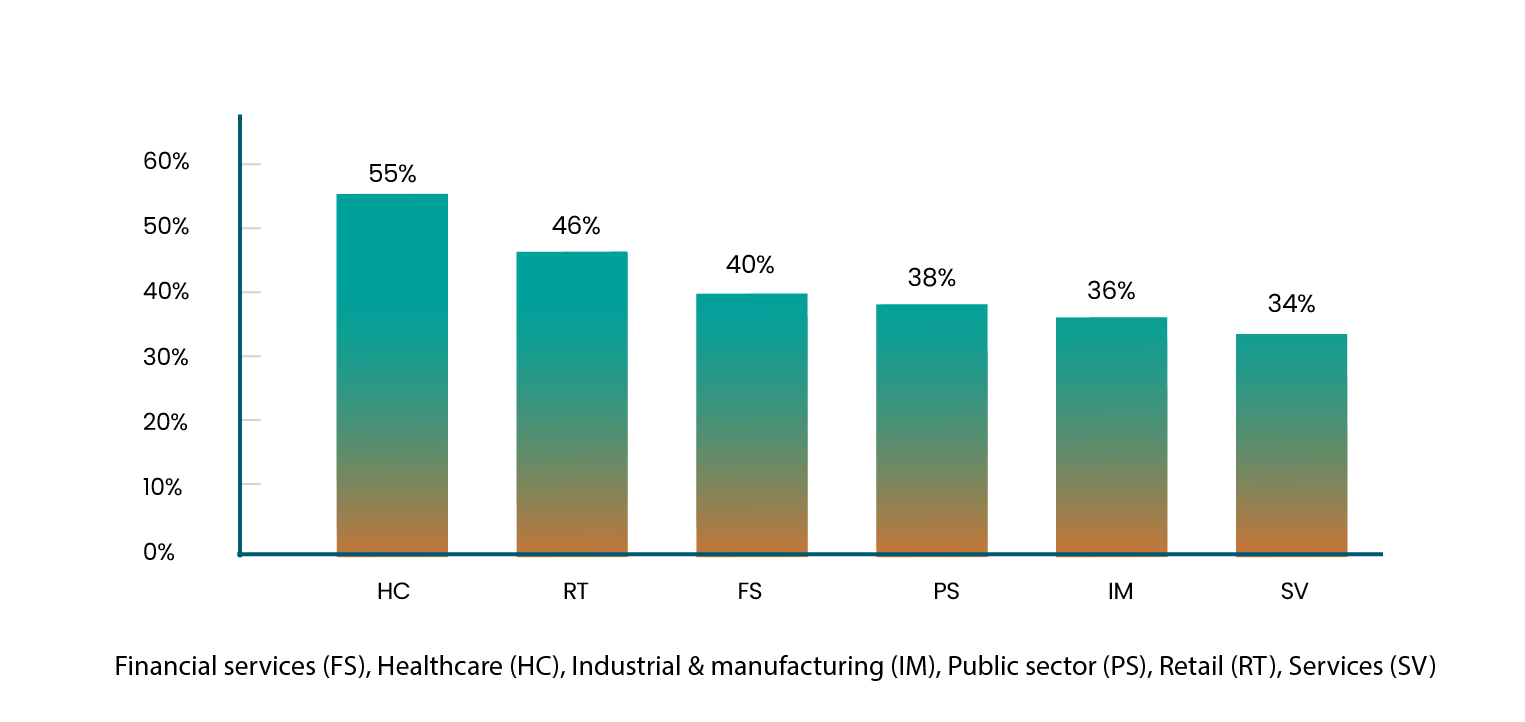
Companies in the public sector are confident that their organizations have secured all certificates and keys.
- Sixty percent of respondents in the public sector say all certificates and keys have been secured.
- Less than one-third (32 percent) of respondents in services and 36 percent of respondents in the retail sector have secured all certificates and keys.
The financial services sector leads when it comes to adopting a zero-trust strategy.
Has your organization adopted a zero-trust strategy?
Healthcare and services verticals are highly effective in protecting digital assets.
- Fifty-four percent of healthcare and services respondents say their organizations are highly effective in protecting digital assets.
Automation – The Way Forward
With digital transformation being the key driving force behind the adoption of digital identity management, automation is being embraced across industries to manage digital certificates.
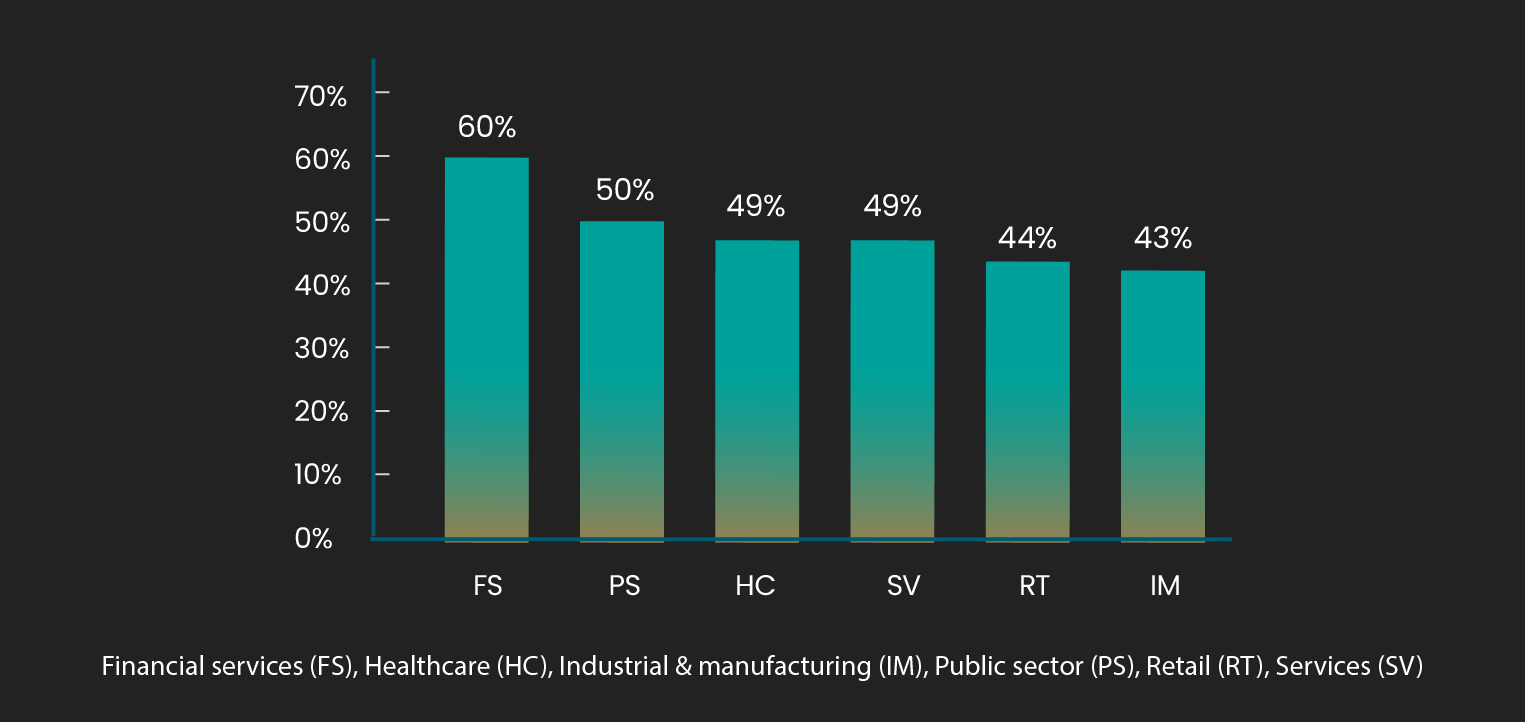
Financial services and the public sector are most likely to automate the management of certificates.
- Sixty percent of respondents in financial services and 50 percent of respondents in the public sector use automation to manage certificates.
- Forty-three percent of respondents in industrial and manufacturing automate the management of certificates.
Organizations using automation to manage certificates
The Importance of Digital Identity Management across Industries
It is not surprising that organizations in the financial services, healthcare, and retail verticals invest more in managing certificates and keys than human identities.
Financial Services
The importance of public key infrastructure (PKI) in the banking and financial services sector cannot be overlooked. PKI is used in several areas, such as their websites, which serve as portals for customers to make financial transactions, and their internal servers, access to which is usually protected with access cards or other PKI-backed services. Firms and functions, which facilitate card-based payments, also comply with another mandated standard – the payment card industry data security standard (PCI-DSS) – and require crypto-services, such as hardware security modules (HSM), to adhere to these standards.
Organizations in the banking and financial services vertical should invest in an enterprise PKI solution ready to take on new opportunities offered by emerging technologies. Automation done right is not just the way forward but also the only way to a future-ready PKI. Your current certificate lifecycle management solution may have many merits, but if it lacks automation or doesn’t have it built-in, it’s forever going to have you running for cover.
Healthcare
While PKI has traditionally been used in hospitals to secure sensitive patient records, cryptography finds new applications in wearable/remote IoT-enabled medical devices. With such devices capturing user information and relaying it back to healthcare professionals by the minute, it is essential to ensure that the line of communication is not intercepted. It is also crucial to keep the device up-to-date via regular updates for optimum security. PKI makes this possible by providing a device identity and a layer of protection to medical devices.
Retail
For a secure and seamless omnichannel customer experience, retailers should invest in an efficient certificate lifecycle automation solution that helps with discovery, renewal, revocation, enrolment, and reporting. An end-to-end management tool provides seamless integrations with certificate authorities (CA) and network device providers, mobile device management platforms, security vendors, and more. It will help you stay proactive by keeping unauthorized users at bay while building digital trust.
Key Takeaways from the Ponemon Report
Automate the management of certificates. Automating certificate and key lifecycle management helps keep digital identities up-to-date and effectively eliminates outages. Processes such as policy management and SSH key rotation can be automated for enhanced security.
Implement structured certificate management processes. Ensure all operations teams have visibility and control over their PKI.
Ensure an accurate inventory of certificates. Employ a comprehensive tool that runs complete, top-down scans across your entire network to discover every certificate. These scans need to run periodically for a healthy inventory free from undocumented certificates.
Public Key Infrastructure (PKI) should be monitored for weak links. It has become apparent that even the best-designed PKIs require supporting systems to help manage them by streamlining certificate tasks, key rotations, and the entire gamut of PKI operations.
PKI must evolve along with the technology it supports. However, due to the sheer scale of applications, PKI requires efficient management. Administrators cannot spend their time manually renewing thousands of certificates, installing them, and ensuring that each one is always online. This will lead to manual errors.
Essentially, every PKI needs to be paired with a certificate management system that can work with it to help execute these tasks.
Build trust. Embrace digital identity management.