Sprinting towards compliance : What’s the BOD all about?
Earlier this quarter, the Department of Homeland Security rolled out Binding Operational Directive 19-02 (or BOD 19-02, for convenience). This directive, applicable to all federal agencies, is part of a prolonged effort by the DHS (and the assisting cyber-security arm, CISA) to enforce digital security and data protection across federally-managed internet-facing systems. In a nutshell, the directive urges organizations to work double-time on remediating network vulnerabilities, effectively cutting the time allotted for these tasks in half.
Why the rush, you ask?
Federal systems are bound to hold copious amounts of critical data. Now, this data could be sensitive, or pivotal to the day-to-day operation of government systems. Hence, haphazard network security maintenance for such systems could be potentially devastating, and here’s why: In network environments, each device or endpoint acts as an individual link in the chain (which represents the network). When something even as trivial as an expired TLS certificate leads to one link being rendered insecure, malicious hackers could use it as a window to compromise an entire network and gain access to terabytes of restricted data. And that’s not a pleasant thought.
What’s more–the threat of data theft notwithstanding, network outages and downtime are detrimental to the health of an organization due to the simple fact it’s online services are rendered temporarily unavailable, diminishing its users’ trust in it.
As should be evident from the CISA’s proprietary network scans (here’s a sample scan from the DHS), SSL/TLS certificate-related issues form the bulk of threats detected in the aforementioned scans, and it’s not hard to pinpoint the cause: every single network component in a system (devices and applications, for instance) requires a certificate to secure its digital identity.
Naturally, the question arises: how can you better manage your certificates to plug the holes in your security setup?
Not just for the bureaucracy
If you don’t work for a federal organization, you’re probably wondering what’s in this for you. Federal agencies have been asked to step up their vulnerability remediation speeds, and for good measure.
However, network security is of paramount importance to private organizations, perhaps even more so than to federal ones. If you run a service, your website probably attracts millions of customers worth of traffic every day. The confidential data of countless clients is stored on your servers, as is sensitive company information. The fact remains that one expired or compromised TLS certificate could wreak havoc to your organization’s operations, either by setting off a chain of downtime on your website(s) or service(s), or by leaking data to malicious actors. This has happened in the past with unnerving accuracy, as you can see here, and here.
The solution: Certificate Lifecycle Management
Certificate-related issues have been singled out as the most common security threat, and here’s why: Certificate infrastructure management is a task that can be manually handled–in theory. After all, once the Certificate Authority (or CA) issues a certificate, all you need to do is generate a private key, and keep tabs on its validity to ensure it’s renewed on time. Right?
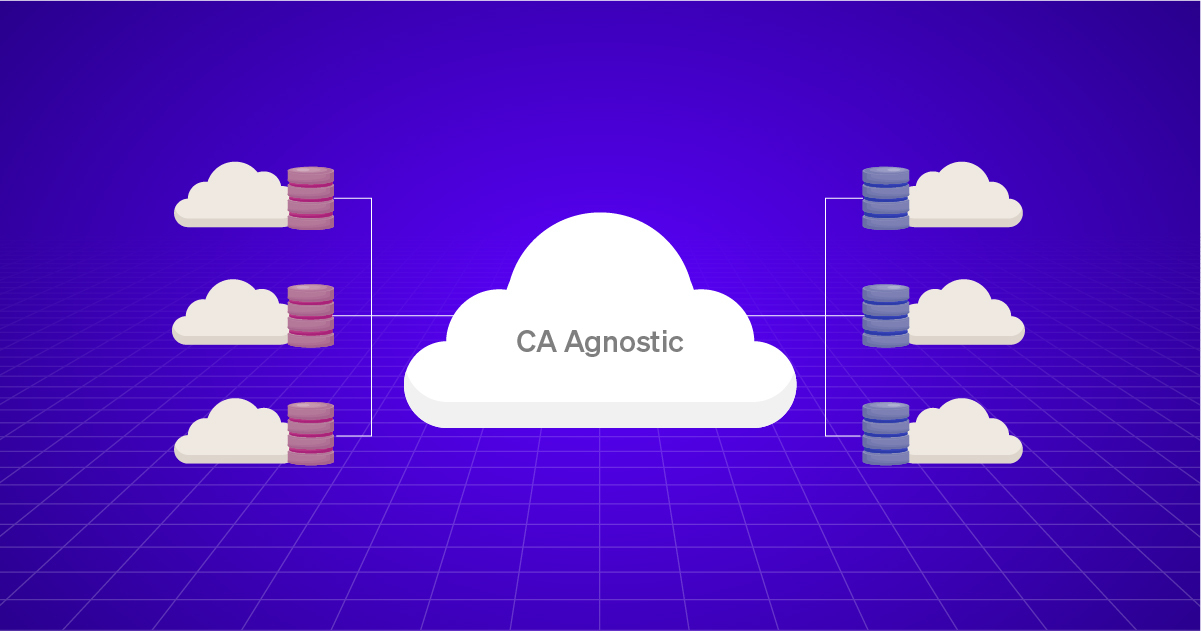
Wrong. As we’ve mentioned earlier, every organization has a lot of certificates. Across multiple cloud environments, and issued by several different CAs, to boot. Keeping track of your certificate inventory on a spreadsheet is an arduous task, and ensuring their security and validity is out of the question. Human error often plagues manual exercises like this one, and the obvious solution is automation.
The certificate lifecycle automation industry is nascent, yet indispensable in today’s increasingly digital world. As their name suggests, these tools burrow into your network environment and act as a single interface from which one can manage their digital certificates, end-to-end. Once a certificate is issued, the management engine kicks in. From that point on, the tool’s GUI can be used to handle every aspect of the certificate, including:
- Renewal
- Revocation
- Provisioning (in multiple devices)
- Location and Discovery
…and a lot more
What’s more, the tool also makes monitoring a lot easier. It automatically compiles graphical reports of renewal statuses, certificate inventories, and so on, providing actionable insights at a glance. And to further diminish human contact with the system, it allows administrators to set up fully automated workflows to carry out maintenance, renewals, invalidations, and a lot more.
A certificate lifecycle management solution is a simple, yet surefire way to render your network free of potentially catastrophic issues, vulnerabilities, and weaknesses.
If we’ve managed to convince you, we’ll give you a head-start on your search for such a certificate management tool. Check out AVX CLM here, to sign up for a free demo, today. Here’s to a future free of certificate-related niggles!