The disruption caused due to digital transformation, cloud migration, and the growing popularity of the hybrid work model encourage business organizations to redefine and reinvent business models to generate consistent revenue streams and maintain relevance in the changing times.

The digital transformation era is characterized by the proliferation of connected devices, virtual machines, containers, and IoT devices. Amid the resulting explosion of the machine identities, like keys and digital certificates, rethinking the cybersecurity strategies is the need of the hour.
While business organizations are trying hard to embrace digital transformation, the consequent security risks cannot be ignored. Securing machine identities across multiple distributed environments has never been more important. According to the 2022 study commissioned by AppViewX and Ponemon Institute, 52 percent of respondents believe that digital transformation plays a pivotal role in driving organizations to adopt a machine identity management (MIM) program to manage the ever-growing inventory of digital identities.
54 percent of respondents invest more in managing machine identities than in human identities. The primary reason backing this decision is that managing the machine identities is crucial in accelerating the organizations’ operational efficiency and productivity, as stated by 61 percent of respondents.
What is the role of machine identities in digital transformation era?
According to Gartner Top Security and Risk Trends for 2021, “As the number of devices increases-and continues to grow-establishing an enterprise-wide strategy for managing machine identities, certificates and secrets will enable the organization to better secure digital transformation.”
Through strong authentication and authorization mechanisms, machine identities help verify all devices, applications, and workloads regardless of where they are, ensuring secure machine-to-machine communication. In doing so, they help build a cybersecurity model that is multi-layered, transparent, location-independent, and, more importantly, based on zero-trust, the bedrock of digital security.
Why do you need to protect and manage machine identities?
Just as humans have usernames and passwords to establish their identity, machines have digital certificates and keys that establish their identity. Every internet protocol (HTTPS, SSH, FTP, etc.) validates and authenticates machine identities to secure network communications.
Discover unknown certificates and keys across heterogeneous environments
Now imagine, if your identity gets stolen, then the imposter will have access to your sensitive and personal information like credit card details, social security numbers, etc. In the same fashion, if the machine identities are compromised, say for instance the device of a banking organization, then the bad actors will have access to critical information of thousands of customers, and they can exploit the data as per their will. The hackers can even acquire administrative privileges and insert malicious codes into the devices and enjoy free lateral movements within the deep network.
The organization that is a victim of such compromised machine identities and encounters data breach is considered non-compliant as per the standard industry regulations and is mandated to pay hefty penalties
Managing the machine identities is critical to data security, integrity, and compliance as it authenticates the communications and ensures that the traffic is encrypted.
What are the risks that can harm your digital transformation initiatives if you fail to manage your machine identities?
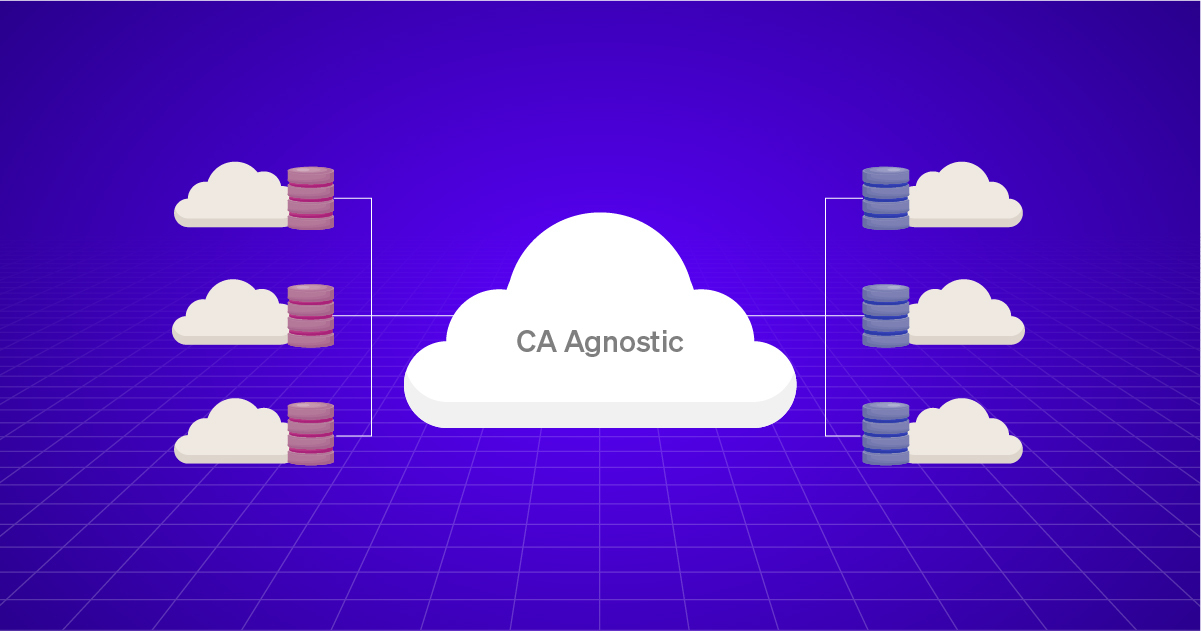
The technological advancements have unintentionally expanded the attack surface of the machine identities. Limited visibility into the vast fleets of machine identities existing beyond the physical boundaries of data centers can jeopardize enterprise security.
Unfavorable situations like compromised certificate authorities (CAs) and digital certificates can lead to system outages and data breaches causing colossal financial and reputational losses. Another major repercussion of a weak machine identity management program can be delayed or slow response time. Detecting system intrusions can be delayed if you don’t know how many certificates are there, where they are located, who their owners are, and other necessary details. The longer a security threat persists, or the compromised machine identity goes undetected, the greater the chance of potential damage.
Machine Identity Management (MIM) in digital transformation era
Digital transformation is a business imperative. Incorporating machine identity management (MIM) is one of the crucial foundational enablers for any digital organization. Frequent high-profile cyberattacks encourage organizations to implement MIM to strengthen their cyber defense.
- Adopt Zero Trust: The Zero Trust framework is based on the principle of ‘trust no one, verify everyone’. In this model, authentication is required for everyone, be it a device or human, trying to access the network. The primary objective of the Zero Trust model is to strengthen the company’s data security while ensuring compliance with privacy laws. You need to restrict data access and verify machine identities before authorizing them access to the systems. Zero Trust must be practiced at every transactional decision point, for instance, when users try to access a device or application, or when a device or a machine communicates with a user.
- Secure digital secrets: With the upsurge in the number of machine identities, security teams must launch identity and access management (IAM) initiatives to secure digital secrets. The secrets can be in the form of usernames or passwords, but now the times are changing, and the passwords are being replaced with credentials related to machine identities, like cryptographic keys and digital certificates. The key-based verification method ensures that access to specific data packets is restricted to authenticated users. By using hardware security modules (HSM), you can generate keys, encrypt and decrypt data and create and verify digital signatures. Public key infrastructure (PKI) and Secure Production Identity Framework for Everyone (SPIFFE) help in safeguarding cryptographic communications.
- Embrace automation: Manual procedures like spreadsheets are not efficient enough to manage and keep a tab on the growing number of certificates across multiple environments. By embracing automation, you can manage certificate and key lifecycle-enrollment, renewal, provisioning, and revocation, and keep your machine identities up-to-date. Automating critical processes like key rotation, policy management, and algorithm upgrades ensures cryptographic agility and eliminate the chance of sudden outages.
- Conduct frequent audits and access control: Auditing machine identities help in identifying the vulnerabilities, like weak passwords, unused keys, and expiring certificates. Addressing these issues on time will help you to improve your machine identity management strategy and keep attacks at bay. By practicing granular access control and role-based access control (RBAC) you can ensure that only the authorized security professional can access the sensitive information.
The key question is – how do you build a strong machine identity management system? Well, it isn’t necessarily complex unless you pick the key pieces, understand the challenges that come in the way of piecing them together, and choose the right approach to resolving them. AppViewX can be a trusted partner who can help you put together an effective machine identity management program.